Are you an Advisor?
Posted on
Working closely with a Chief Information Security Officer (CISO), an Advisor will have a strong blend of technical ability, communication skills and cyber security experience. An advisor supports the risk identification and management process across all aspects of Information Technology for a business, government agency or educational institution. Responsibilities include assessing the current adequacy of the security strategy, business continuity /disaster recovery plans, threats to the systems, and then calculating the impact of potential adverse events. Audits and assessments must be continual, as the threat profiles change constantly.
The Advisor will keep executive management up to date on the results of the risk assessment and make recommendations for mitigations, or projects, to protect their systems or cover potential losses.
To continually improve the quality of the risk management, some advisors collect lessons learned information and metrics from security events and integrate the knowledge gathered into future protection strategies. This may involve reviewing logs, network traces and other evidence from computers, networks and data storage devices.
Senior Advisors use their knowledge and experience to examine systems and procedures to identify potential adverse events, including hardware and software crashes, physical disasters, malicious intruders, malware, denial of service attacks and employee misconduct.
Analysis will include a clear description of the risk and its likelihood. For those considered significant, an assessment of the impact, in dollars or business disruption will be developed. From this, mitigation plans must be developed and presented to management for approval and funding.
Links with CyberEPQ Modules
- 8. Operational Information Security Management and Security Architecture
- 10. Introduction to Audit Compliance and Assurance, Cyber Essentials and GDPR Risk Assessment Management
- 11. Risk Assessment and Management and Information Security Governance and Management
What does an Advisor do?
The advisor’s role is to identify risks which might occur thus making it essential for advisors to stay knowledgeable of current advances in all areas of information technology concerning vulnerabilities, security breaches or malicious attacks. Advisors will continuously evaluate communication security, data vulnerability, business continuity and compliance risks whilst identifying vulnerabilities or weaknesses in systems. Part of their role will also be to examine employee compliance with security controls and deficiencies as well as evaluating security policy, processes and procedures for completeness.
It is essential that advisors also ensure that controls are adequate to protect sensitive information systems and report to management on IT system vulnerability and protection against malware and hackers. This will need to be clearly documented with defined risks and potential impacts along with the statistical probability of such an event and identify systems affected by the defined risk.
Advisors will also provide mitigation/ damage reduction proposals with cost justification as well as assist in identifying breaches in a firm’s security or tracking the source of an unauthorized intrusion. Resulting in Advisors identifying defensive steps to take, including necessary firewalls, security software and data encryption as well as recommend all infrastructure and applications patching and remediation that may need to be done. The advisor will also communicate recommended business continuity preparations and controls, including deficiencies, to business units and recommend improvements in network security, identity management and logging.
What are companies looking for?
- Knowledge and ability to deal with Cyber Security threats & vulnerabilities; plus, appropriate countermeasures
- Demonstrate a good understanding of cyber security attack techniques and threats
- Ability to quickly identify indication of compromise and take appropriate action to mitigate or eradicate
- Possess a high level of capabilities of research and data collation
- Relevant degree or industry qualifications would be preferable such as, CISSP, CISA, CISM, CEH or OSCP
UK Earning Potential
Upwards of £40,000 depending on geography, experience and definition *
* source: Indeed March 2020
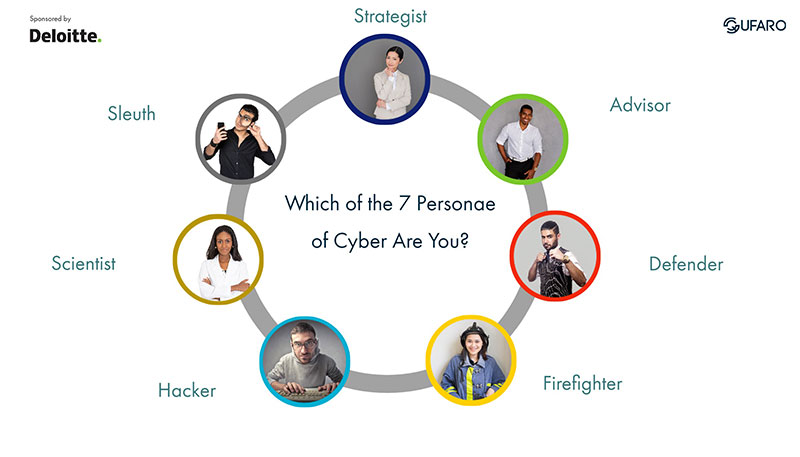
Learn more about the Seven Personae of Cyber